
The Ultimate Guide to Cybersecurity for Cloud Video Surveillance & IP Security Cameras
November 29, 2021

Cybersecurity is becoming an increasing priority for enterprise organizations. Because cybersecurity deals with data, privacy, and security, organizations today are finding that cybersecurity and physical security—especially video surveillance—are unavoidably linked.
But what exactly do you need to worry about when it comes to cybersecurity and video surveillance? How can you protect your video security system against breaches and cyberattacks? How do you know that the data privacy of your employees, customers, and more is secure?
This guide will help you understand what good cybersecurity standards and practices look like in a video security context. You’ll learn what best practices you personally can follow and what best practices you should look for in a vendor.
For a step-by-step guide to evaluating and improving your system's cybersecurity, download these free checklists.
Why is cybersecurity important for video surveillance platforms?
Most physical security professionals agree that cybersecurity is a top concern. According to a survey conducted by Rhombus Systems, 81.1% of respondents ranked cybersecurity as “high or very high priority”.
Cybersecurity is especially important for video security systems because video surveillance by its nature typically includes sensitive or private data. Many organizations use security cameras exclusively for safety and security purposes. People being recorded expect that footage of them will be used in a security context and kept private. This is especially important for security systems that include biometric data such as facial recognition.

Cybersecurity is also about trust. When you protect your data, you also protect the privacy and maintain the trust of everyone in your organization and everyone who interacts with your organization.
Cybersecurity best practices for enterprise video security
So, what does “good” cybersecurity look like for enterprise video security? This section cover what proper cybersecurity standards look like in a video security context.
There are two sides to cybersecurity for video surveillance:
- Best practices for you as the end-user
- Best practices for your vendor
Though there are some things you can personally control, the most important way to protect yourself is by choosing the right vendor. For this reason, we’ll go over best practices that your organization can follow, and also go over best practices that vendors should be following. This will help you perform due diligence with a better understanding of what proper cybersecurity standards look like.
Are there formal certifications around cybersecurity and video security?
There are no formal certifications that pertain specifically to cybersecurity and video surveillance. However, there are several relevant certifications that do matter:
NDAA Compliance
The National Defense Authorization Act (NDAA) bans U.S. government agencies, contractors, and grant or loan recipients from using products manufactured by certain companies, primarily due to cybersecurity concerns.
In all cases, it’s highly recommended to use hardware that is NDAA compliant. If you’re going through a vendor, they should be able to confirm that they use components for cameras, sensors, and other devices from whitelisted sources only.
Learn more about NDAA compliance and video security here.
SOC 2 Compliance
Developed by The American Institute of Certified Public Accountants (AICPA), SOC 2 is a set of information security policies and procedures specifically created for service providers that store customer data in the cloud.
If you plan to use a cloud-based solution (as opposed to an NVR system with onsite servers), it’s important to use data centers that are SOC 2 compliant. This ensures that while your data is processed in the data center, it is protected by the strictest cybersecurity protocols.
Cybersecurity, privacy, and compliance for video security

SOC 2 and NDAA pertain to the state of your system itself and are directly related to video security. However, there are likely additional regulations around privacy that your organization is already following. These standards also apply to video surveillance.
For many of these regulations, you’ll likely find that video security systems can be used as a tool to help you reach or maintain compliance. For example, for HIPAA, security cameras can be used to record and track who has physical access to protected patient data. If you plan to use video surveillance as part of your compliance strategy, your vendor may have experience and can help you navigate this.
Cybersecurity best practices for users
1. Protecting system access with user permissions
System access has to do with how you set up your system roles and permissions. The idea is to control access to sensitive data and reduce the damage and scope of a potential breach.
Best practices include:
- Make sure only trusted individuals have system access
- Limit access to only those who need it
- Extend exactly as much access to an individual as they need, no more.
For example, nonprofit UACDC gives staff members access to different security camera feeds based on job functions. Their security staff can view all camera feeds, but don’t have admin permissions. Meanwhile, employees can view camera feeds in the areas they supervise. For example, a staff member who teaches computer literacy might have access to the cameras in the computer lab and other classrooms, while a staff member who supervises sports might have access to gym and outdoor cameras.
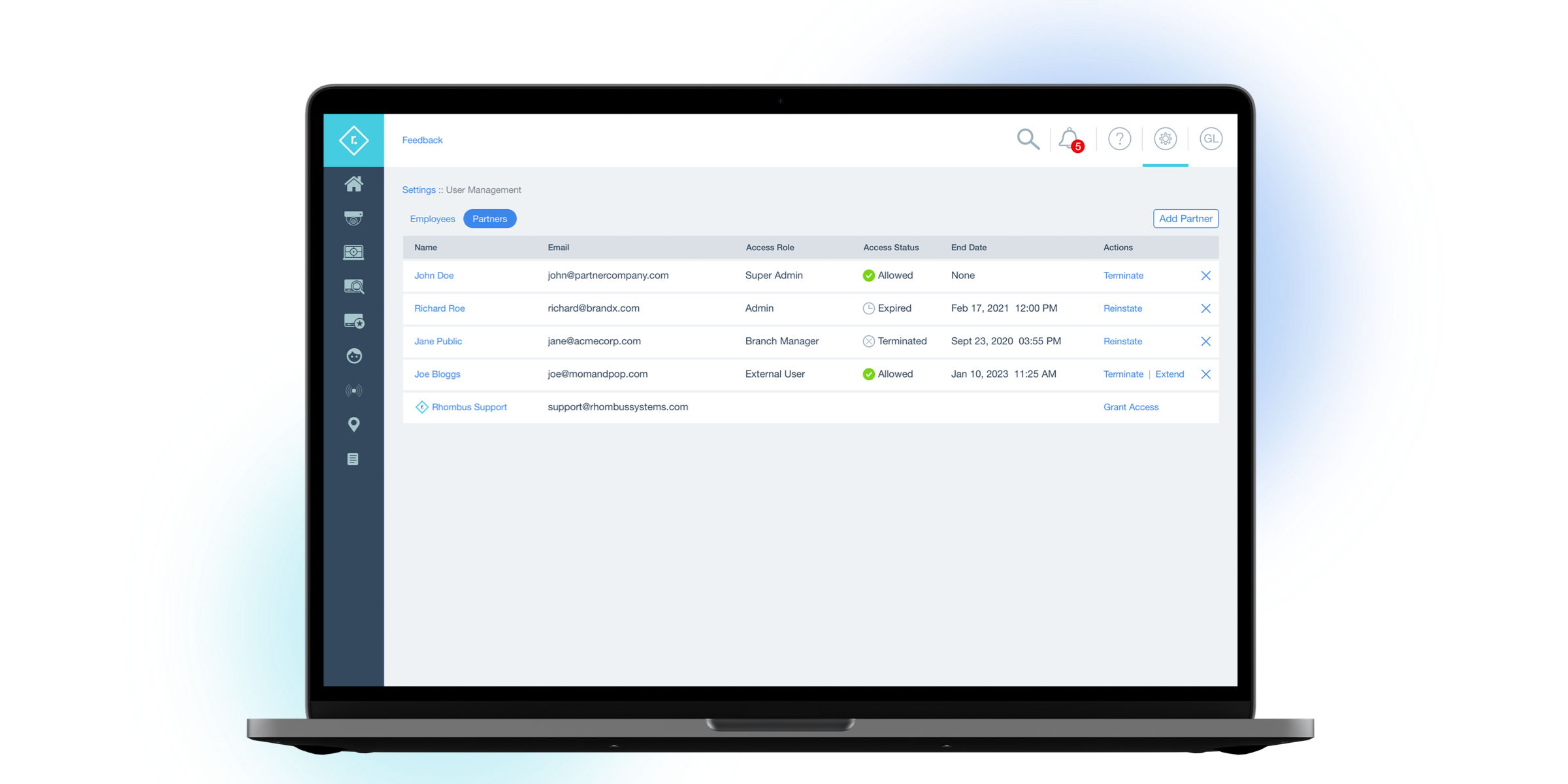
Setting up granular user permissions like this is both more convenient from an operational point of view and safer from a cybersecurity point of view. Staff members can quickly access exactly what they need, without having to sift through irrelevant information. The impact of breaches on an individual level is kept to a minimum, because leaks are limited to the data accessible by the exposed individual.
With this in mind, it’s important to use a video security system that has role management and location management, and supports customization of roles and permissions.
2. Password management and privacy
Most enterprise organizations have guidelines around secure password management. These guidelines extend to your video security system.
Best practices can include:
- Strong passwords
- Two-factor authentication
- Single sign-on
- Using a system that monitors for anomalous logins
To further protect sensitive information, use configurable privacy masks. These privacy masks let you black out specific pieces of video, such as computer monitors, to prevent private information from being recorded by cameras. Many video surveillance systems include this feature, and privacy masks can help you maintain compliance with regulations around private data, such as HIPAA or CJIS.
3. Employee training
Even systems that are highly secure from a technical standpoint can be vulnerable to social engineering attacks or improper handling of sensitive data. It's important to create policies and procedures on the handling of private and sensitive data, including video footage and biometric data.
Anyone in your organization who has access to sensitive or private data should receive cybersecurity training. Training should include:
- Proper handling of sensitive data, including video footage
- How to remain in compliance of relevant regulations (such as GDPR, HIPAA, CJIS, BIPA, CCPA, and PCI)
- Proper password management
- How to defend against social engineering attacks
Cybersecurity best practices for your vendors
When it comes to cybersecurity and video surveillance, one of the most important steps you can take to protect your organization is choosing a reliable vendor. Even if you follow best practices on your end, your organization is vulnerable to cybersecurity breaches if your provider isn’t secure.
So, how do you choose a secure vendor? This section will help you understand what good cybersecurity standards look like on the provider side, so you can better judge who to partner with and feel confident about your security partner.
1. End-to-end encryption
Encryption protects data by encoding (or “scrambling”) it in a way designed to make it impossible for intruders to understand.
Because video security systems collect a lot of private information, it’s crucial to protect all data—in all media forms—with encryption.
This includes:
- All media is fully encrypted with redundancy
- All video is encrypted
- Complete end to end encryption with all data encrypted both at rest and in-transit
- All communication with the cloud (if applicable) is encrypted
2. System access best practices
To properly protect your privacy and your security, it’s crucial that only you, the end user, control access to your data. Your security platform should be designed in a way that makes it impossible for anyone—including your vendor—to access data without your explicit permission.
This means:
- Only authorized end users have the authority to initiate and provide account access
- All granted access is logged and can be revoked at any time
- Your vendor does not have any form of super admin account that allows access to customer accounts
- Vendor employees have limited access to necessary systems and are required to use two-factor authentication
Learn more about privacy and access here: Putting Customer Privacy and Security First.
3. Third-party security audits
Third-party security audits help companies find and address cybersecurity issues that they may otherwise be unaware of.
Your video security provider should perform regular third-party assessments. This increases system security, helps keep cybersecurity protocols up to date, and demonstrates a certain level of dedication to protecting customer data. If you want to review a vendor’s third-party audits, most will provide reports on request.
4. Automatic security updates
For modern video security solutions, best practices include automatic security updates. These are signed firmware updates that happen regularly and automatically, with no input needed from your organization.
Automatic security updates ensure that:
- Your organization is always protected by the most advanced and up-to-date cybersecurity protocols
- You’re never relying on out-of-date technology to safeguard your facilities
- There are no gaps in protection due to delays on the user end—once new updates are ready, they happen right away with no action required by your organization.
5. Track record and past cybersecurity experience
When evaluating vendors in the context of cybersecurity, it’s helpful to look at past performance. Check for a history of breaches, attacks, or data leaks.
If a physical security vendor has a history of cybersecurity breaches, it’s a dealbreaker for many enterprise organizations. 38% of surveyed physical security professionals report being unlikely or very unlikely to work with a vendor that has experienced a cybersecurity breach, while 36% say they evaluate vendors on a case-by-case basis.
If you are considering a vendor who has experienced a breach, extra precautions are in order. Consider: 1) how recent the breach(es) was, 2) the extent of the damage, 3) what steps have been taken to fix cybersecurity vulnerabilities, 4) if you trust the team to prioritize cybersecurity best practices in the future.
Technical best practices
This section goes into more detail about the technical aspects of what a secure video surveillance system looks like.
1. Hardware & Camera Best Practices
- All video is encrypted
- No open inbound ports
- Automatic, signed firmware updates
- All communication with the cloud is encrypted
- Protection from man-in-the-middle attacks; e.g., mutually authenticated client and server-side certificate verification
- Protection against unauthorized physical access
2. Cloud Infrastructure Best Practices
- Hosted on SOC 2 compliant data centers with internal and external access isolated
- Complete end-to-end encryption with all data encrypted both at rest and in-transit
- All passwords are stored using strong one-way hashing algorithms
- All media is fully encrypted with redundancy
- Audit logging from internal and external clients is kept for all access
- Protection against denial-of-service attacks
- Multi-tenant security
- OWASP security guidelines are followed
3. Application (Mobile Apps and Web) Best Practices
- All communication with the cloud is encrypted
- Protection from man-in-the-middle attacks; e.g., mutually authenticated client and server-side certificate verification
- All logins are monitored for anomalous logins
- Regular third-party security audits are performed
- Locked down certificate trust stores
Conclusion
For modern enterprise organizations, a physical security strategy is incomplete without also considering cybersecurity. By following this guide, you can better understand what proper cybersecurity practices look like in a video security context and set your organization up for security and success.
If you're interested in secure video surveillance for your organization, Rhombus can help. With decades of cybersecurity experience and a pristine track record, Rhombus protects your data so you can enjoy complete security and peace of mind. Learn more by requesting a personalized demo or reaching out to one of our team members at sales@rhombus.com.

Try Rhombus for Free!
See why school districts, cities, and Fortune 500 companies use Rhombus.
Start Trial

